MITM Attack Detection (Python Project)
2025-10-29
Cybersecurity
Python Project
ARP Spoofing Detection
MITM Prevention
Network Security
ARP Scanner
Security Analysis
A Python-based security tool that detects ARP spoofing and ARP cache poisoning attacks in local networks using IP–MAC verification.
MITM Attack Detection
A Python-based security tool to detect ARP Spoofing and ARP Cache Poisoning attacks in Local Area Networks.
Download Project
Click below to download the Python-based MITM Attack Detection tool.
Download MitmAttackDetection.zip (Python Program + Manual)View on GitHub
Project Screenshots
Project Requirements
- Python 3.8 or above
- Scapy module (for ARP handling)
- Administrator privileges for ARP table access
- Compatible with Windows / Linux systems
- LAN environment required for sniffing ARP packets
Key Concepts & Features
- ✔ MITM Attack Detection using real-time ARP monitoring
- ✔ Identifies ARP Spoofing and ARP Cache Poisoning
- ✔ Detects mismatched IP–MAC pairings
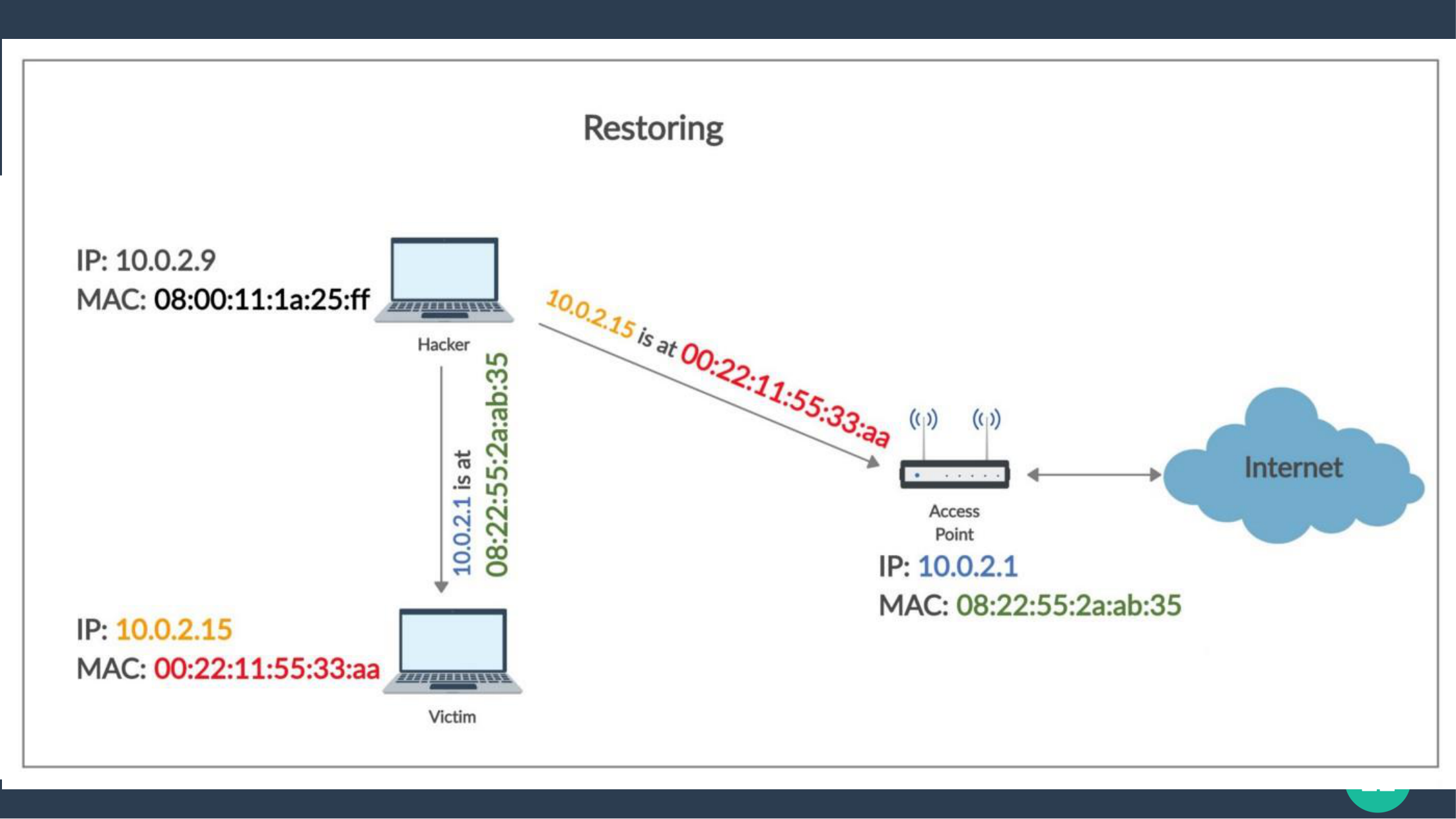
- ✔ Manually verifies real MAC addresses via ARP request
- ✔ Alerts user when an attack is detected
- ✔ Python-based lightweight tool, easy to run and extend
Understanding MITM & ARP Spoofing
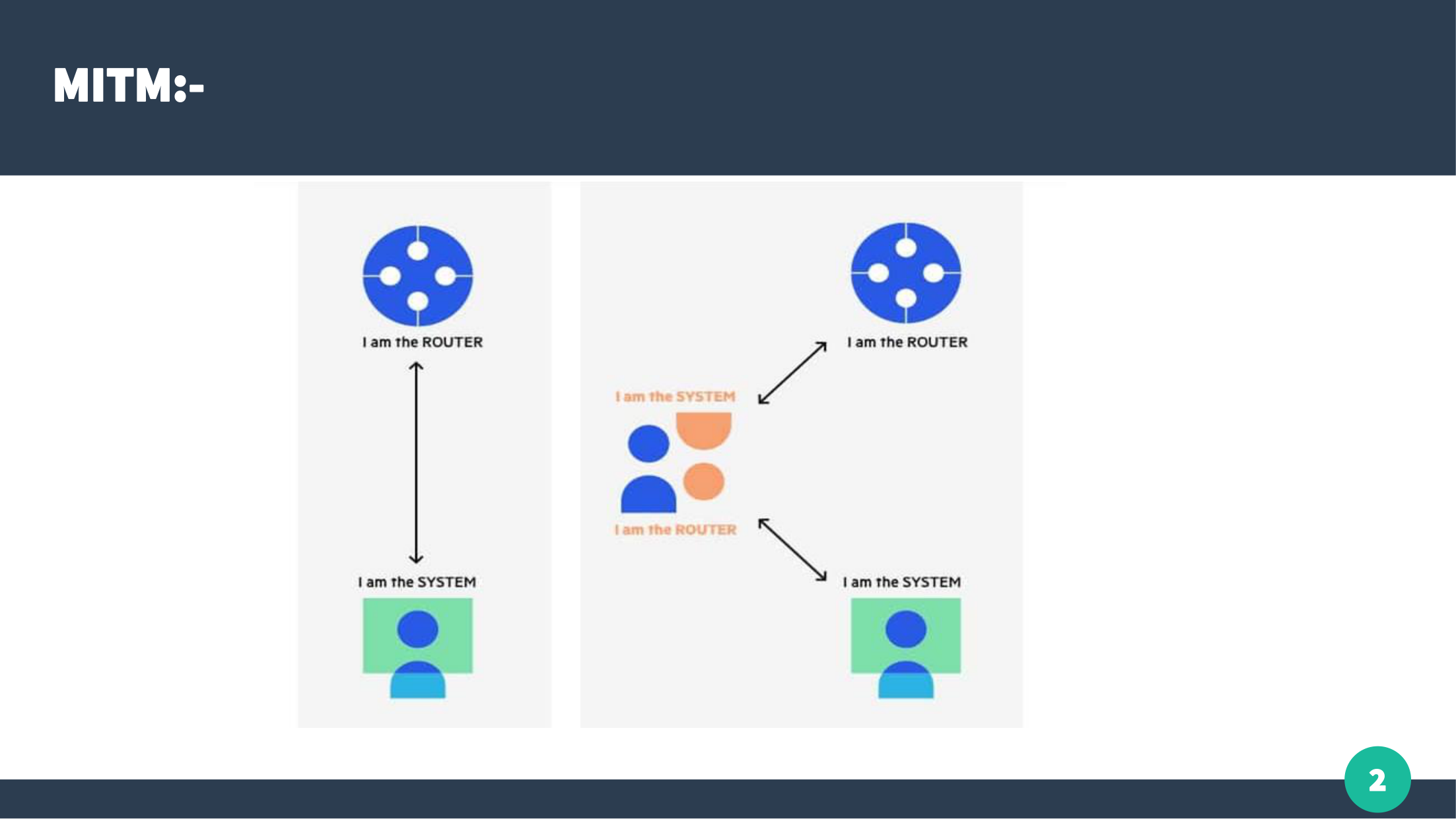
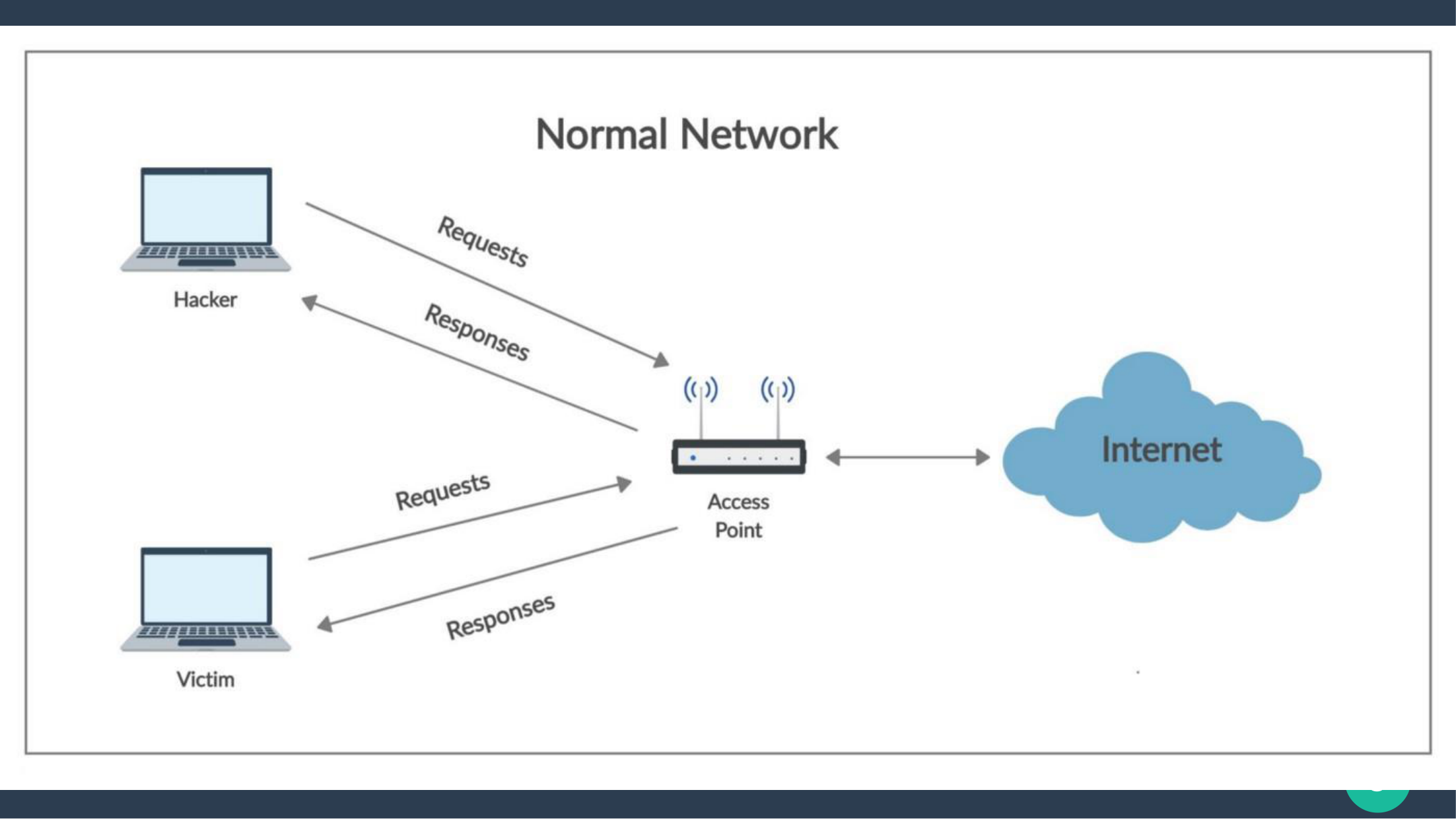
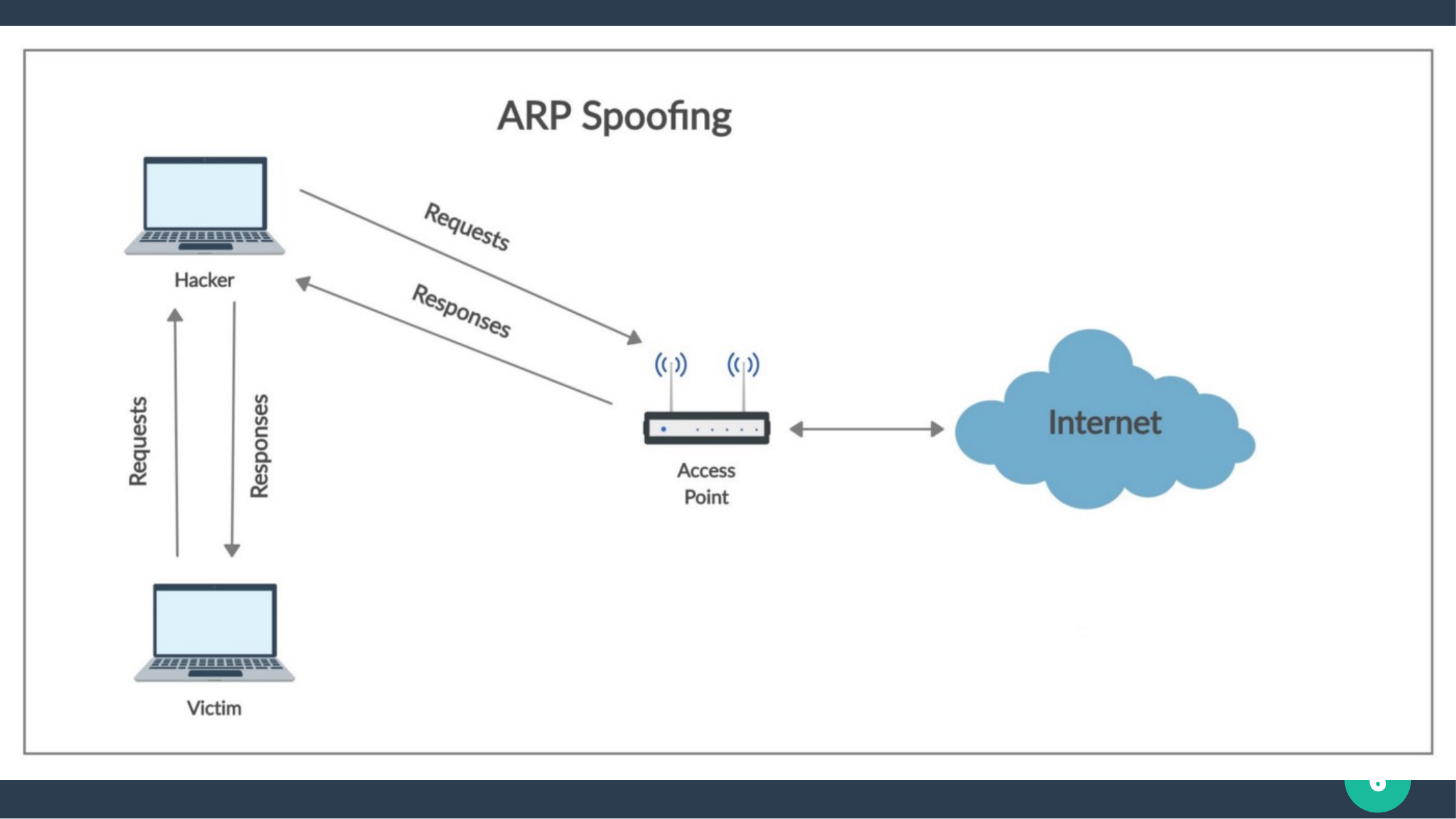
MITM (Man-In-The-Middle):
An attacker secretly intercepts and relays communication between two devices
pretending to be the legitimate endpoints.
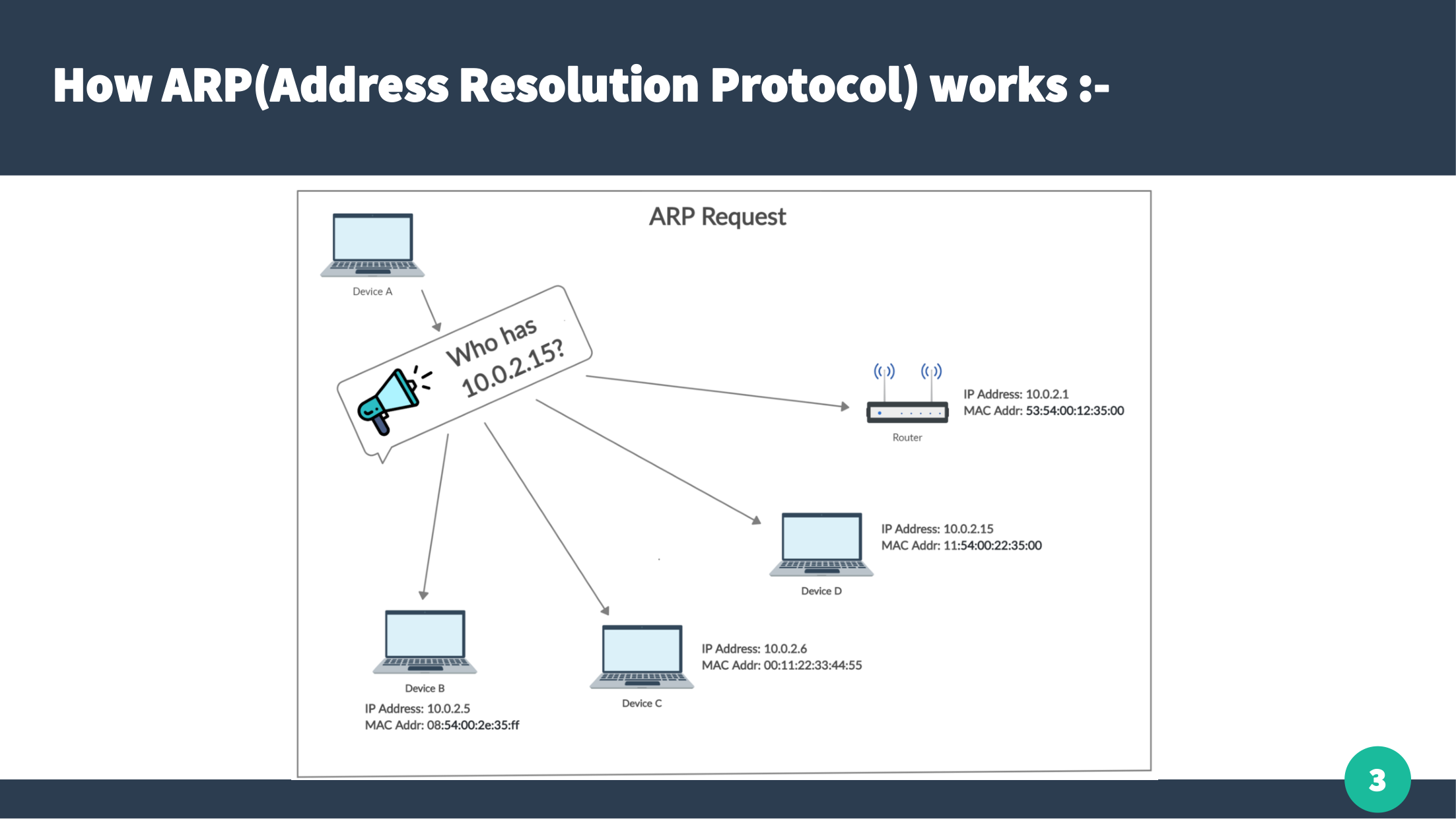
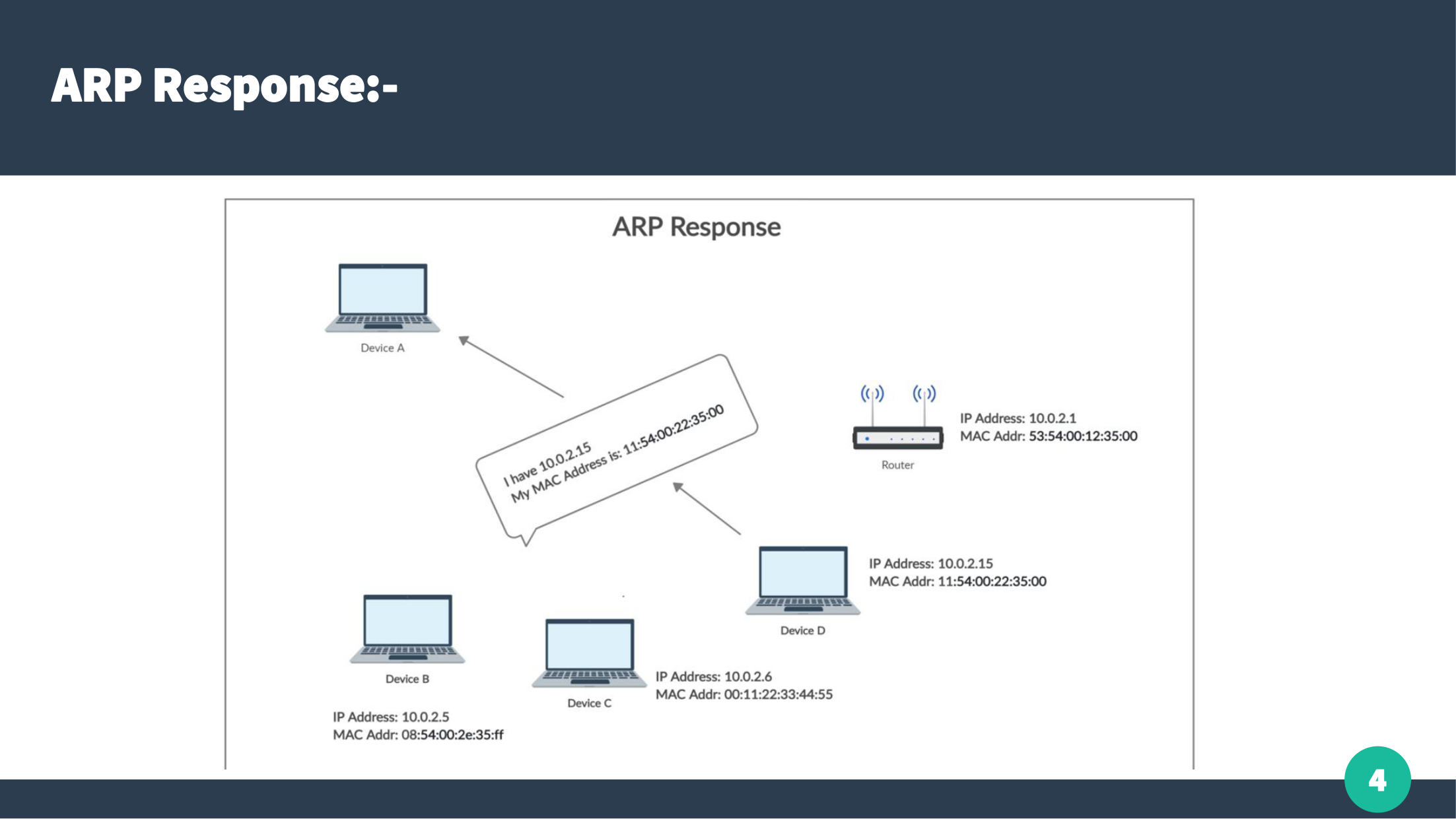
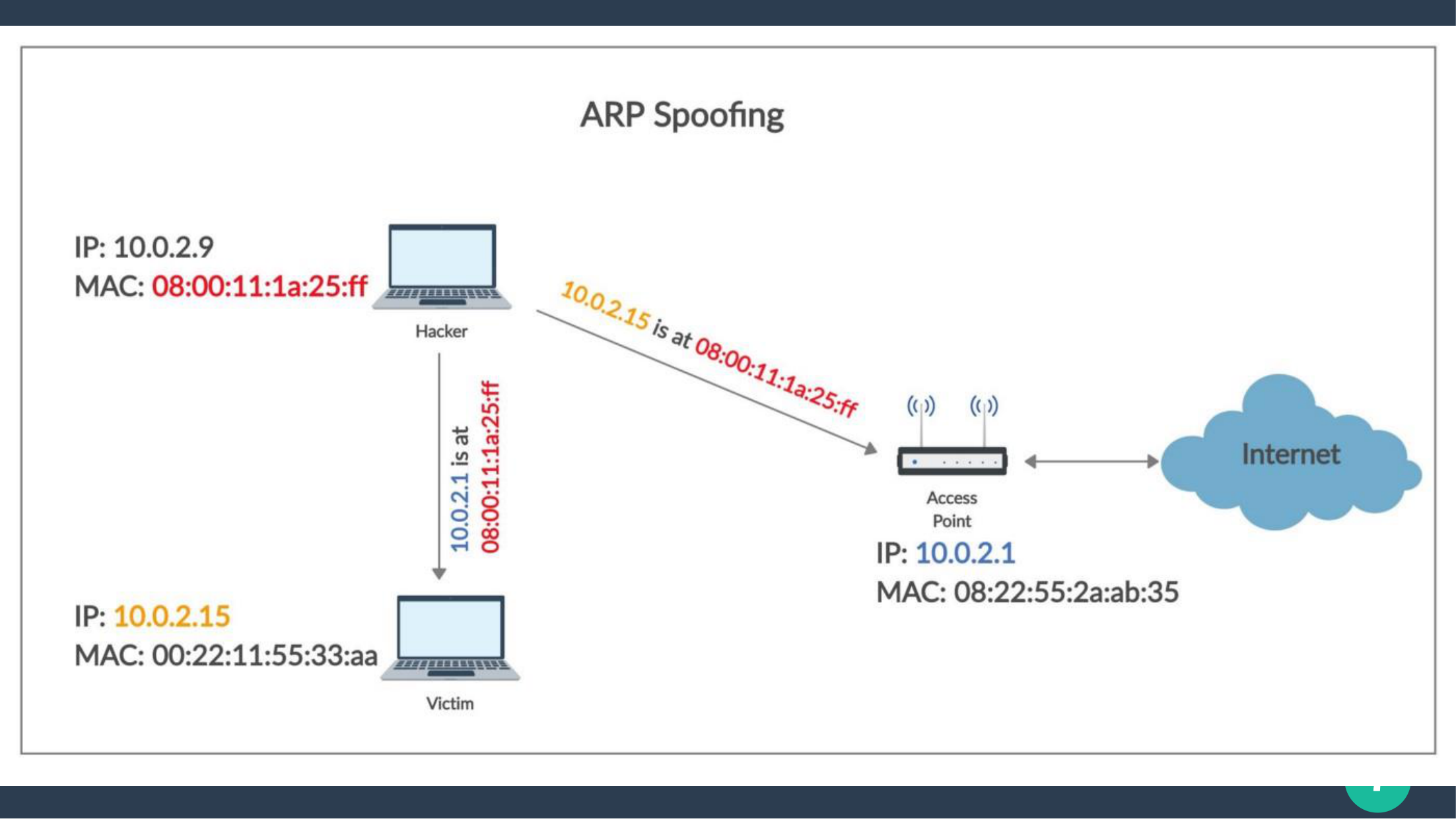
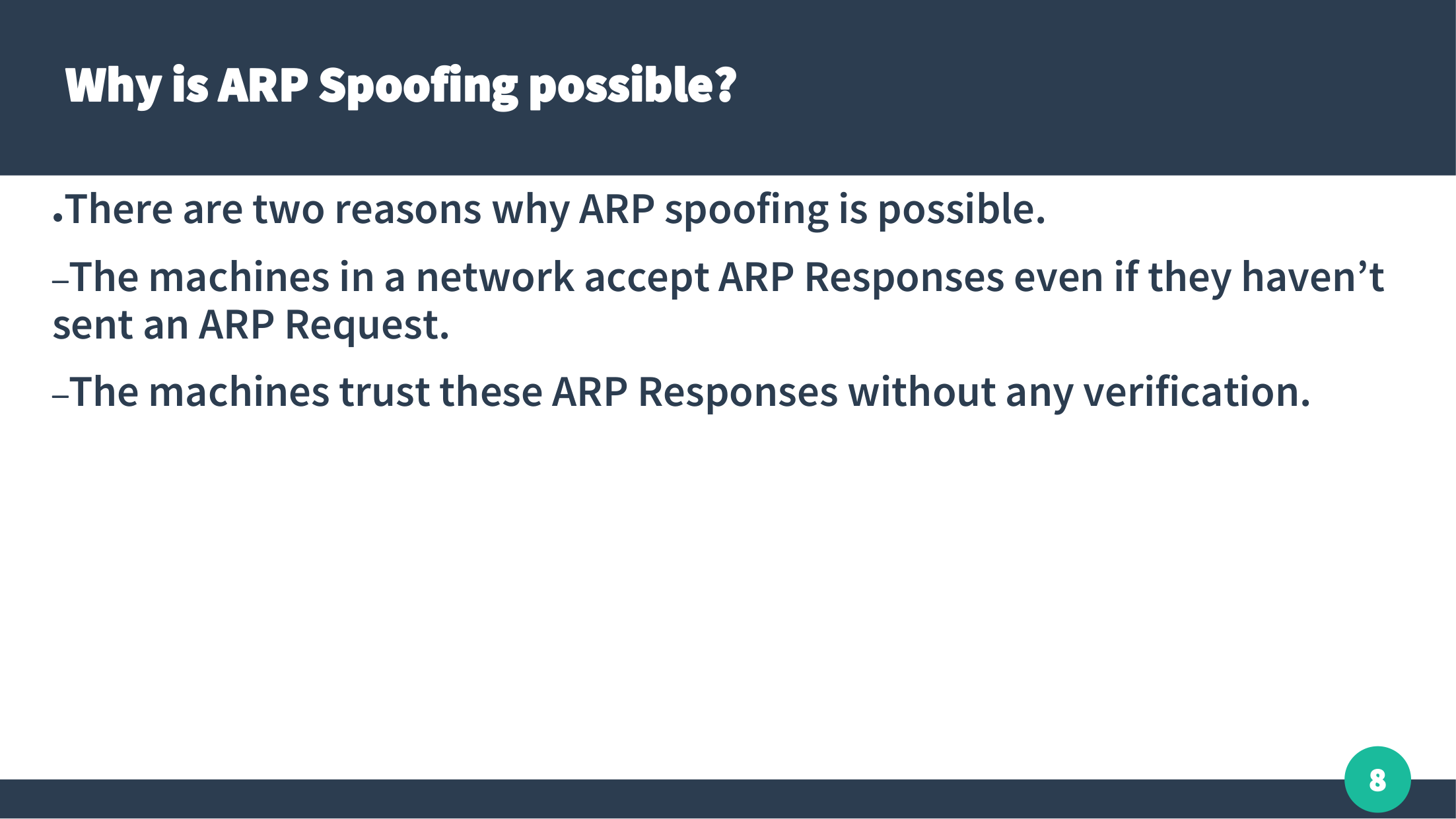
Why ARP Spoofing Works:
1. Devices accept ARP responses even when they never requested them.
2. Devices trust ARP replies without any verification.
Common Terms:
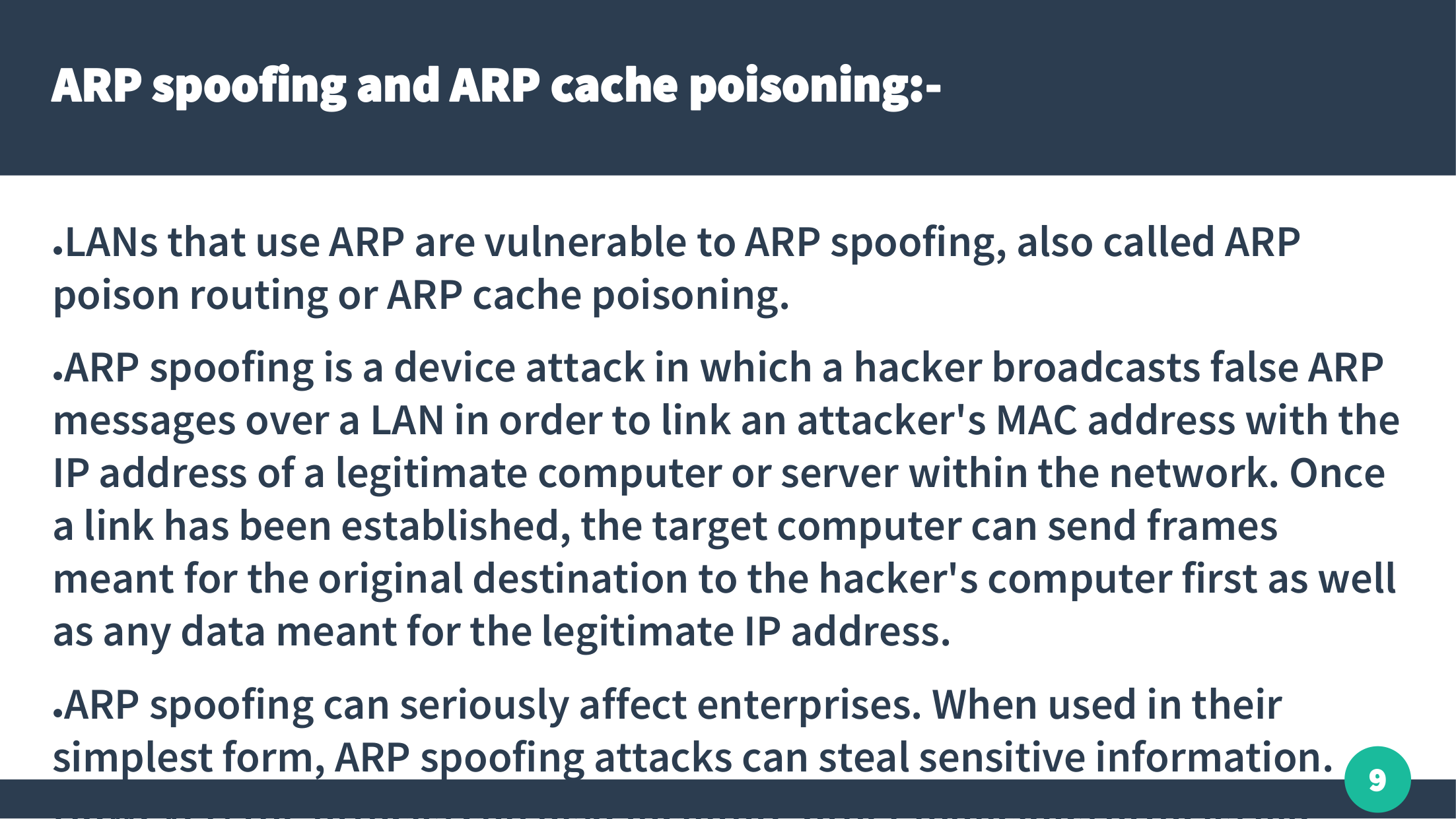
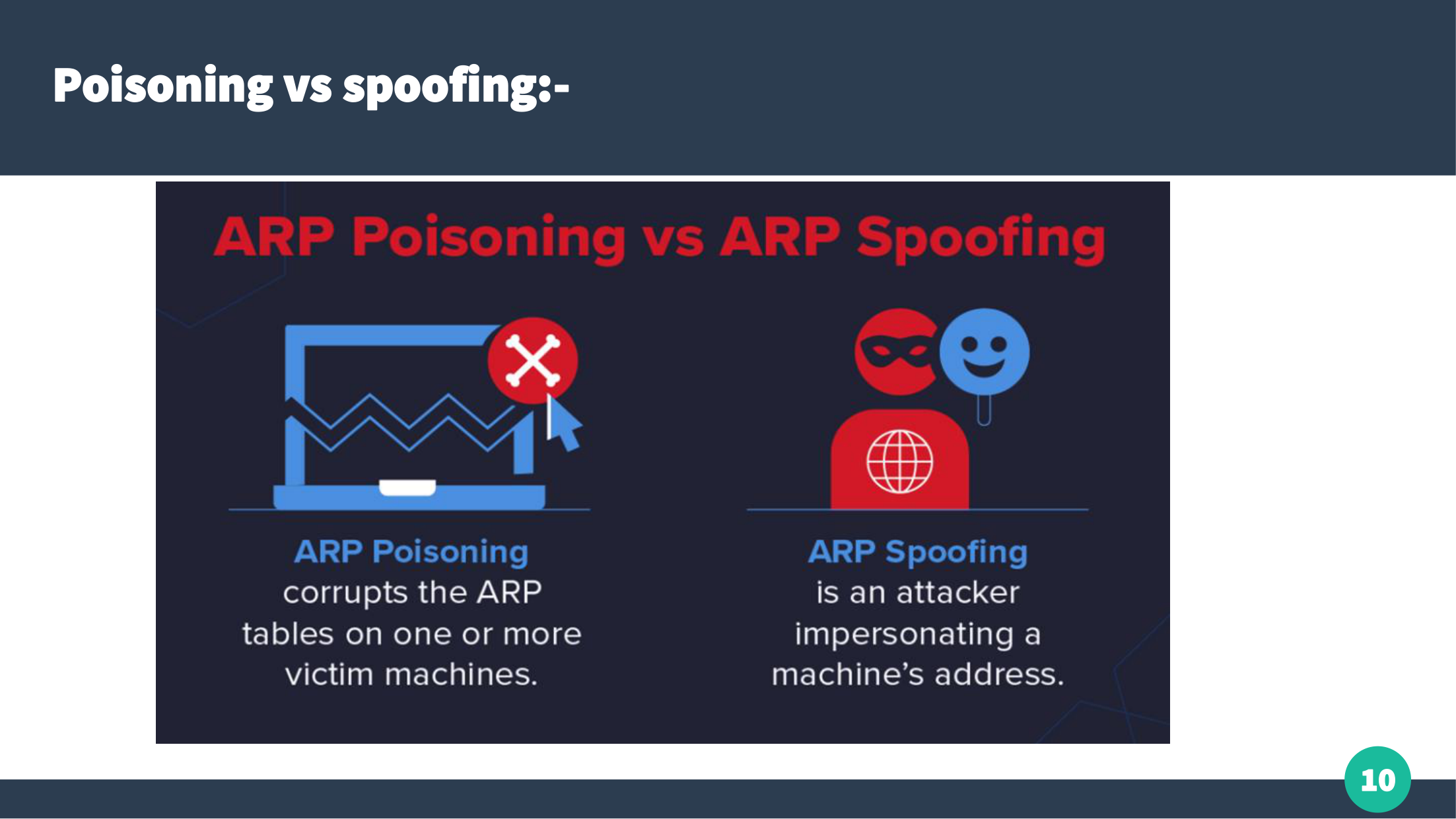
- ARP Spoofing → Sending fake ARP replies
- ARP Cache Poisoning → Forcing a victim to update its ARP table with fake entries
Threats Caused by ARP Spoofing
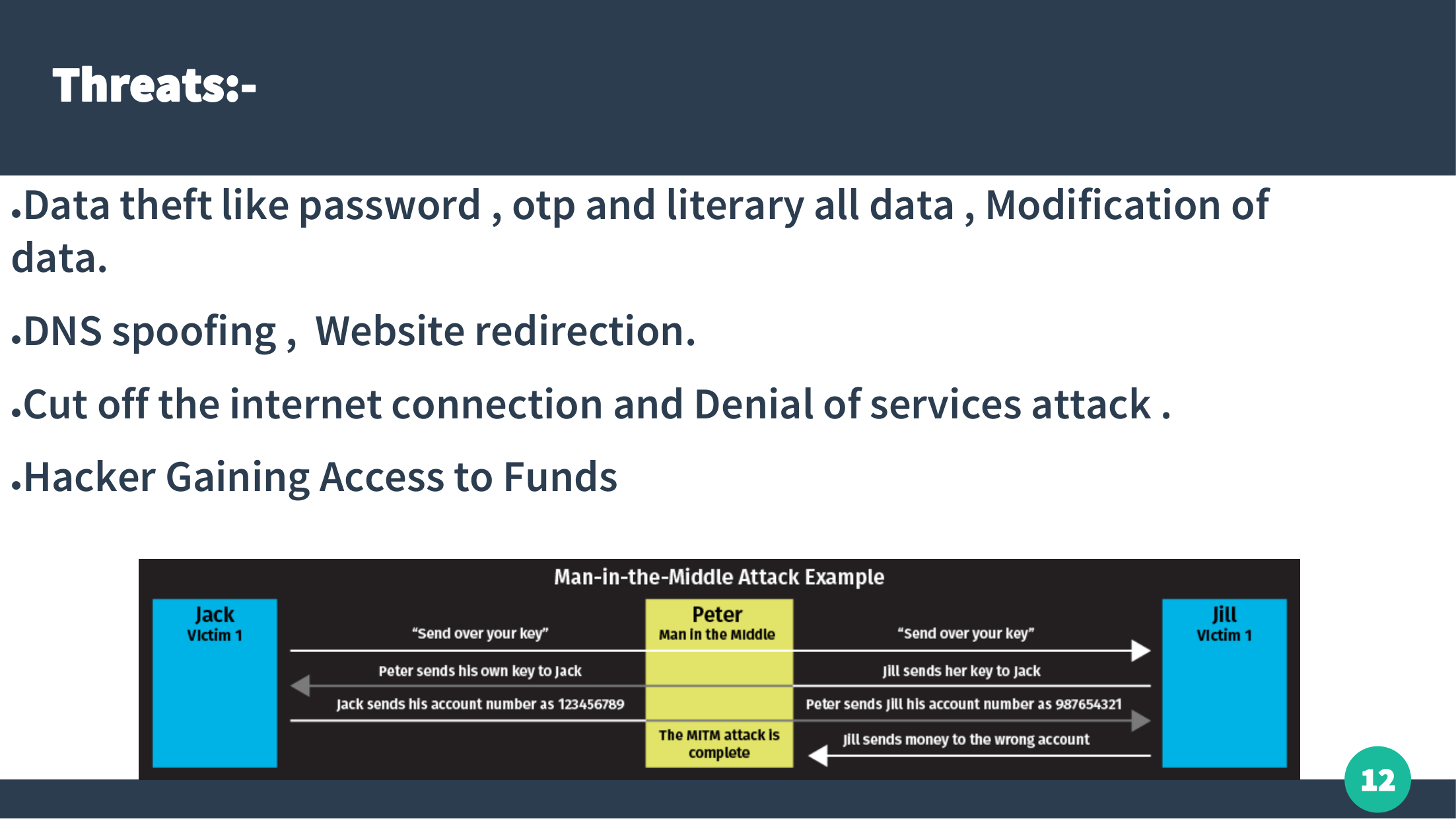
- ✔ Theft of sensitive data (passwords, OTPs, private messages)
- ✔ DNS Spoofing & website redirection
- ✔ Internet disconnection and Denial of Service
- ✔ Unauthorized access to accounts & funds
MITM Attack Detection Algorithm
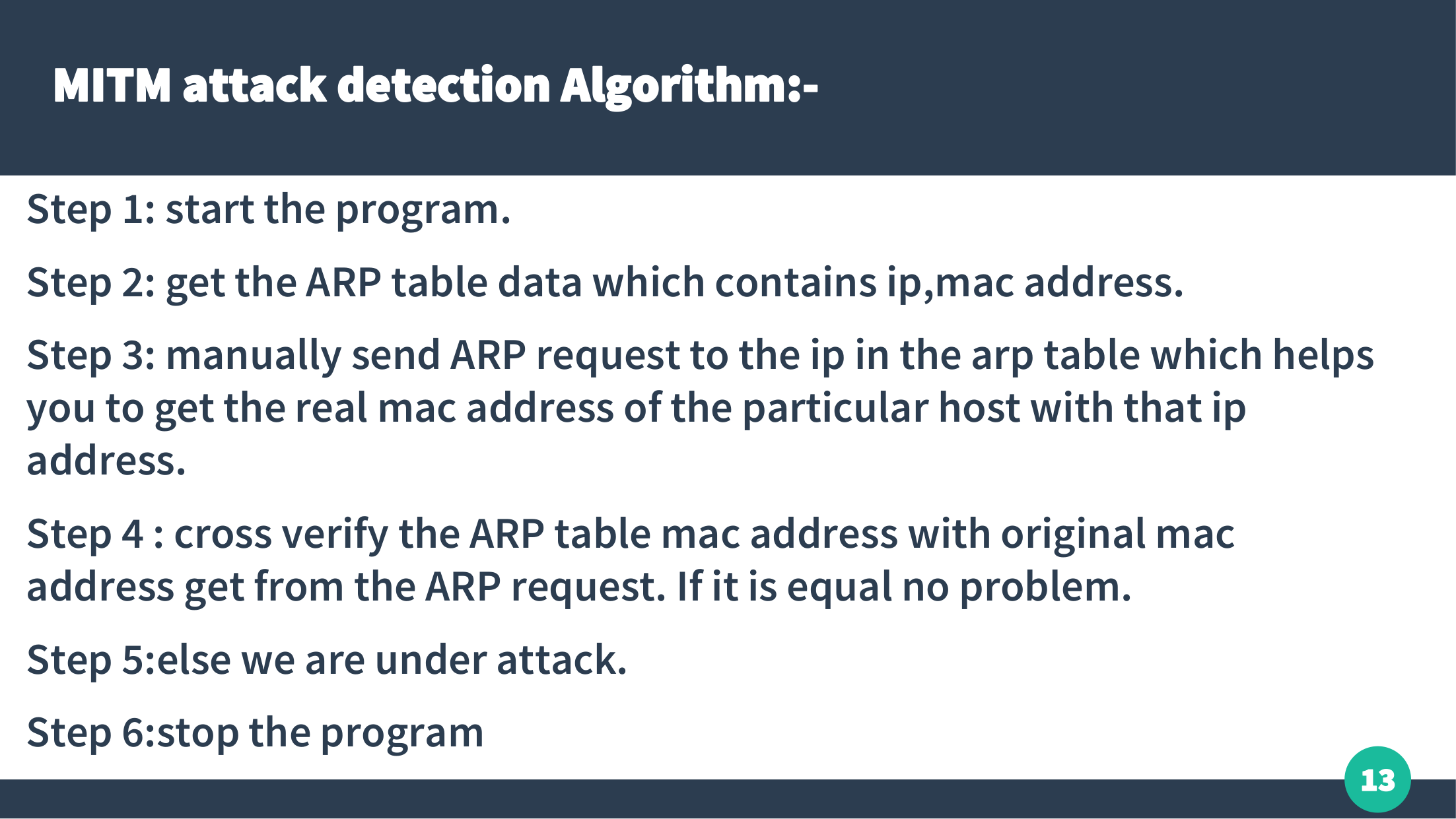
Step 1: Start the program.
Step 2: Read ARP table entries (IP + MAC address pairs).
Step 3: Send ARP requests manually to each IP in the table.
Step 4: Compare original MAC address with ARP table MAC.
Step 5: If mismatch → MITM attack detected.
Step 6: Stop the program.